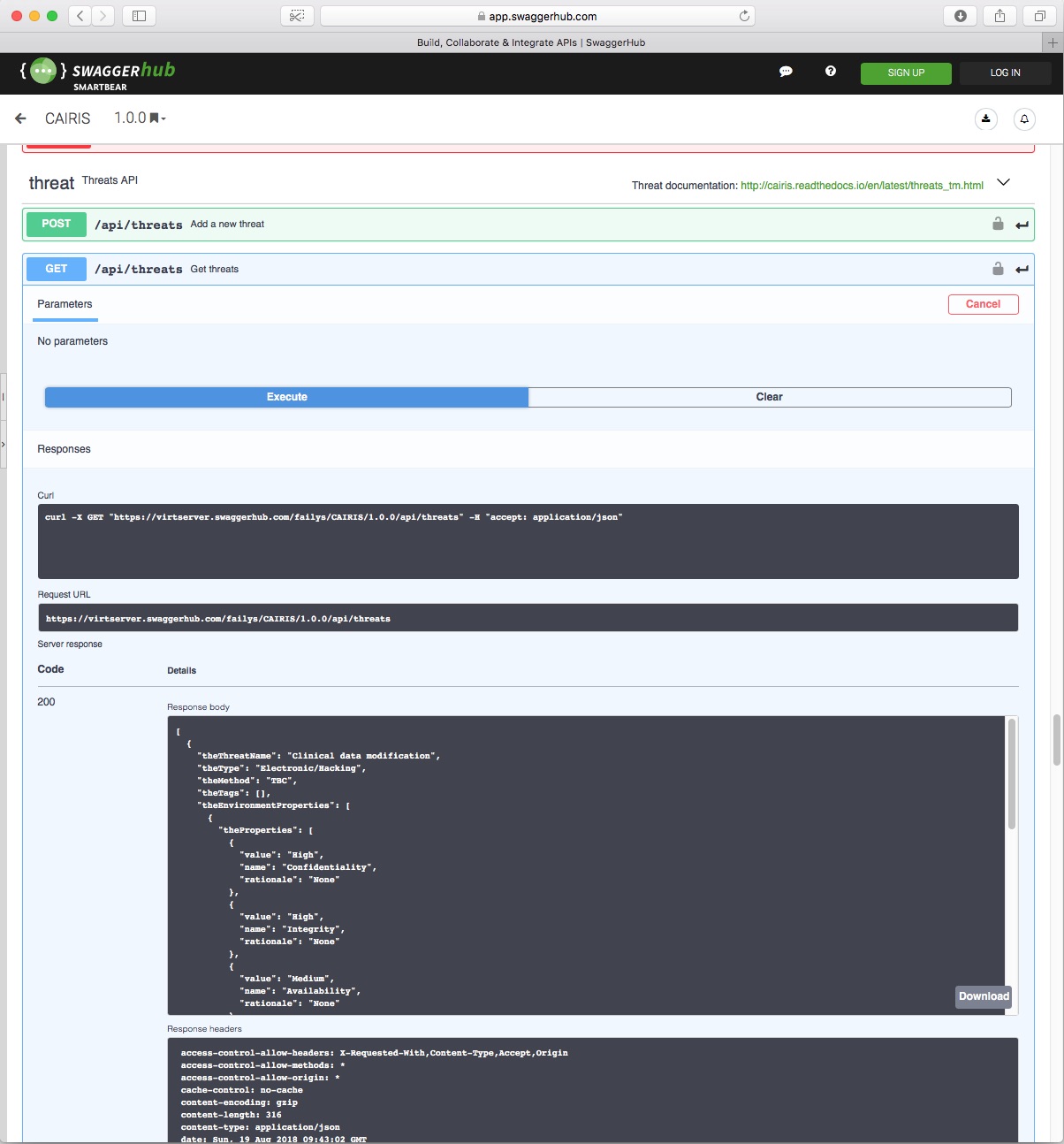
Manage your security, usability, and design artifacts in one place
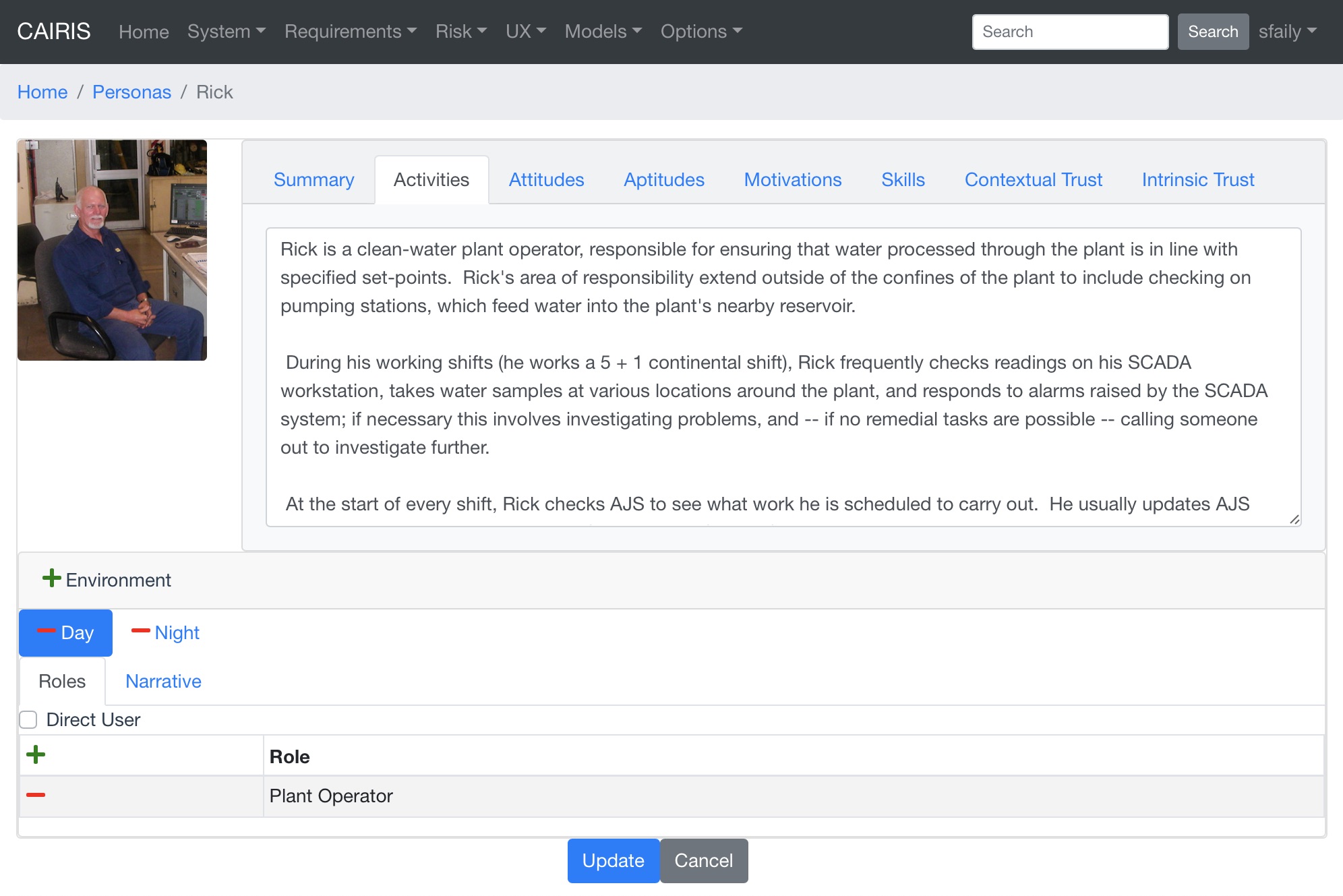
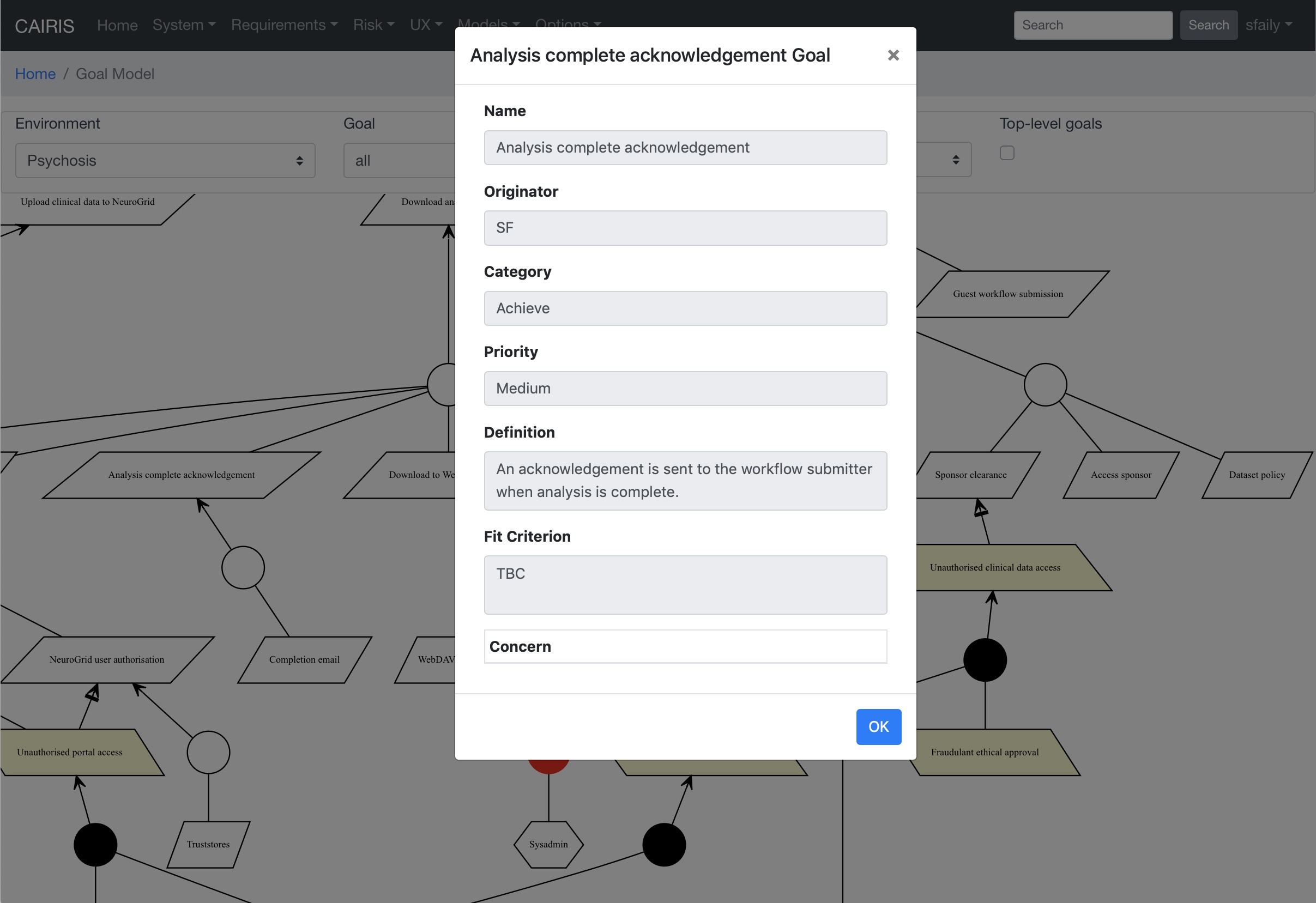
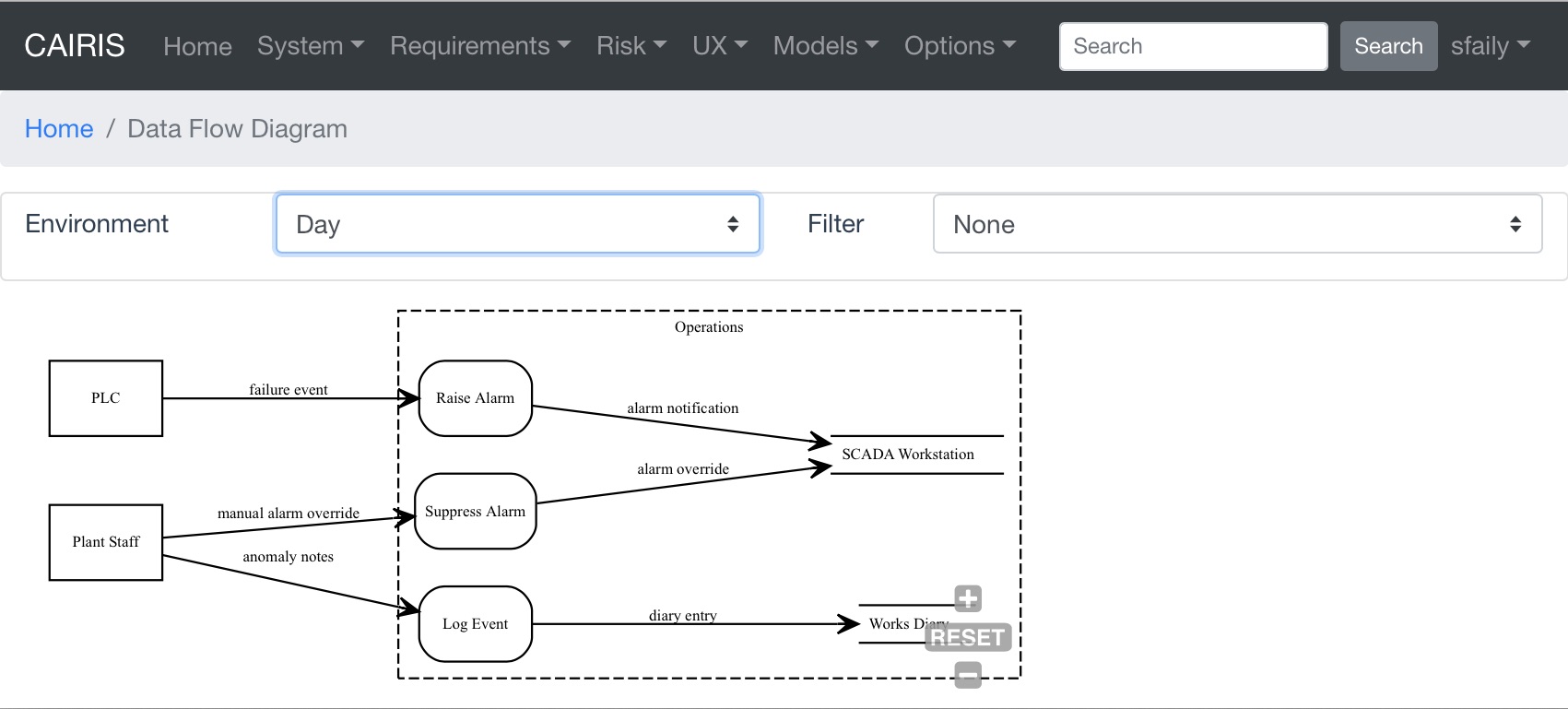
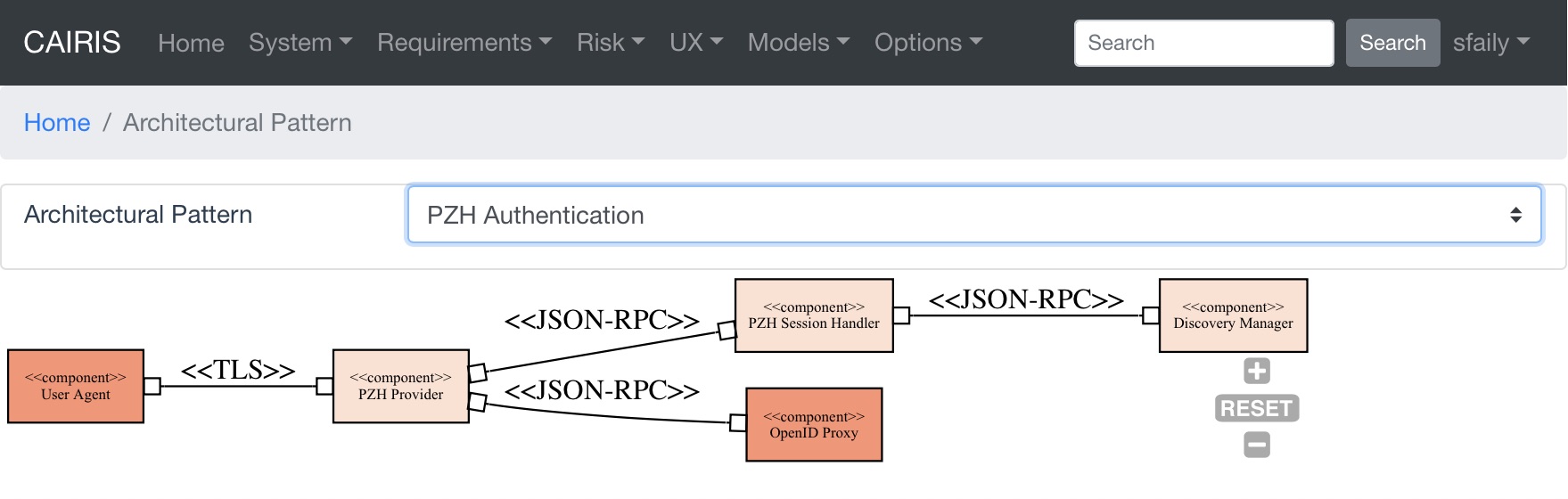
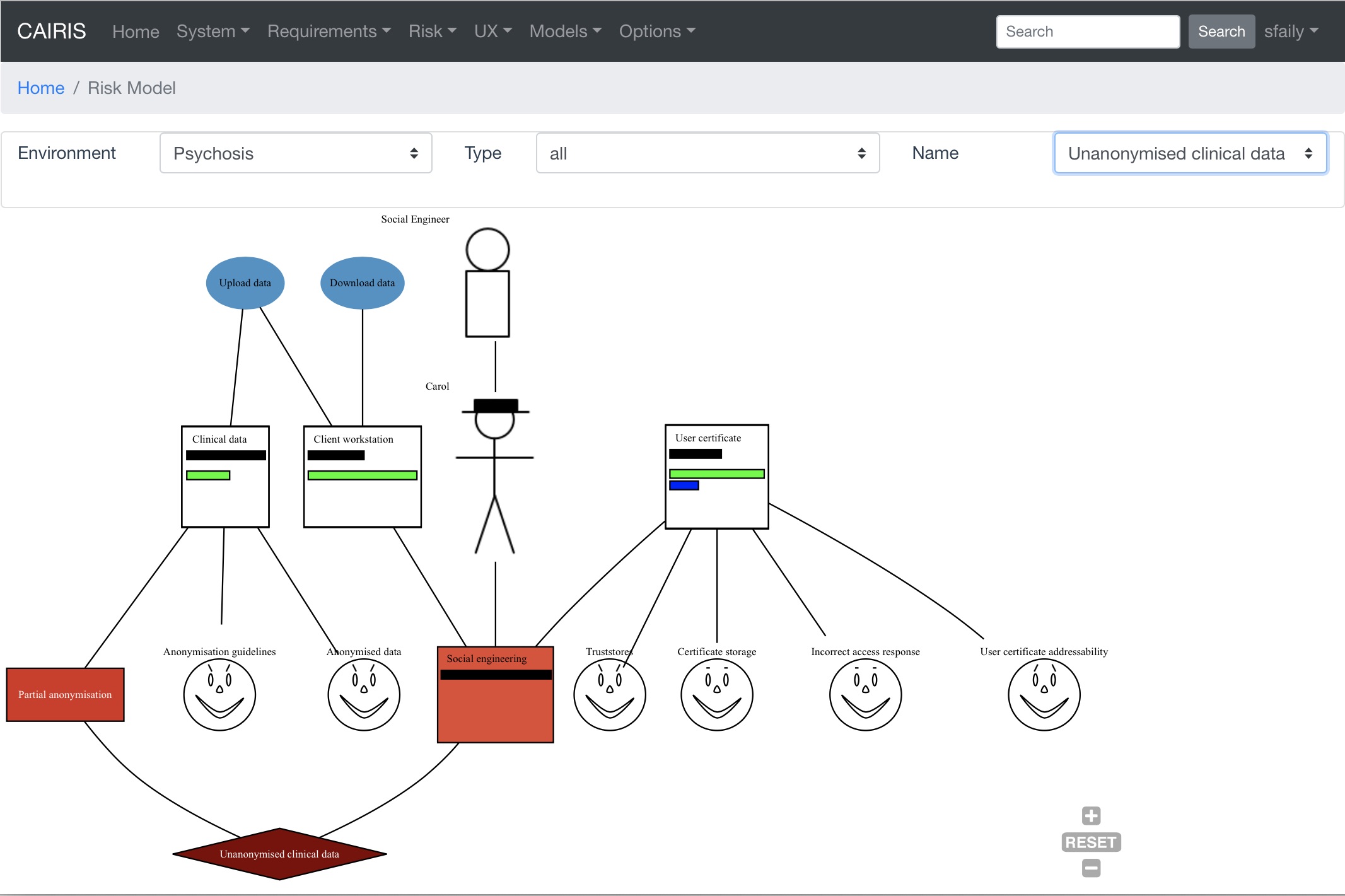
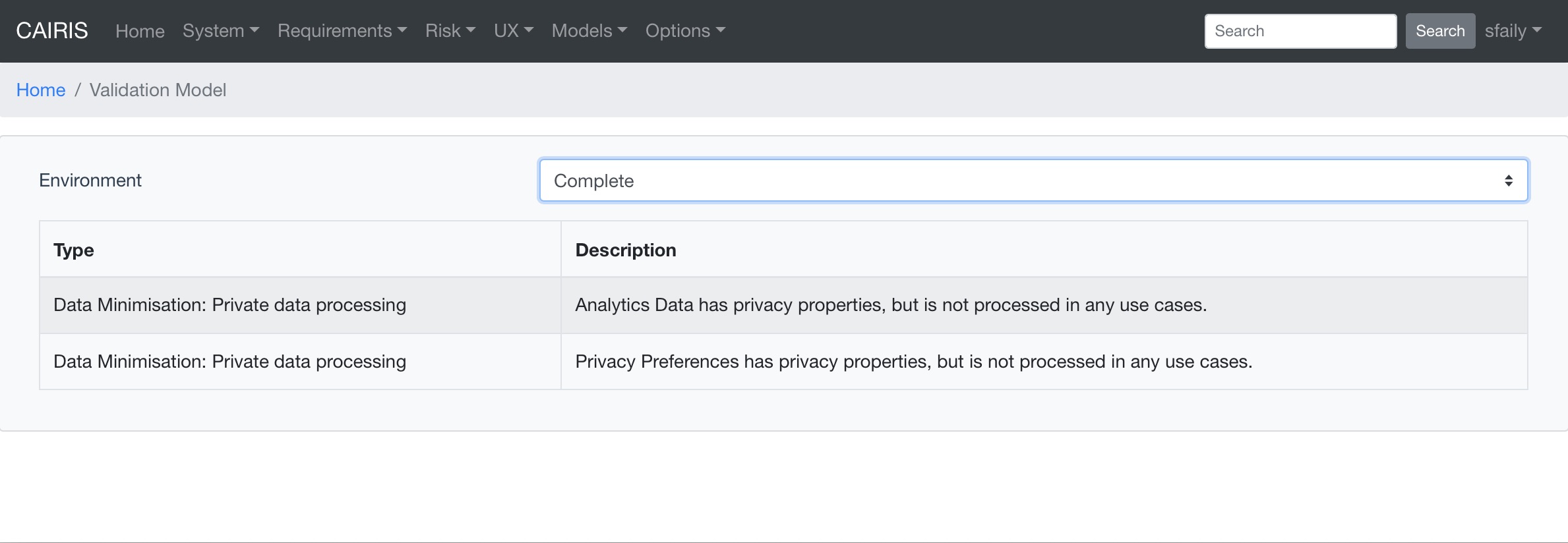
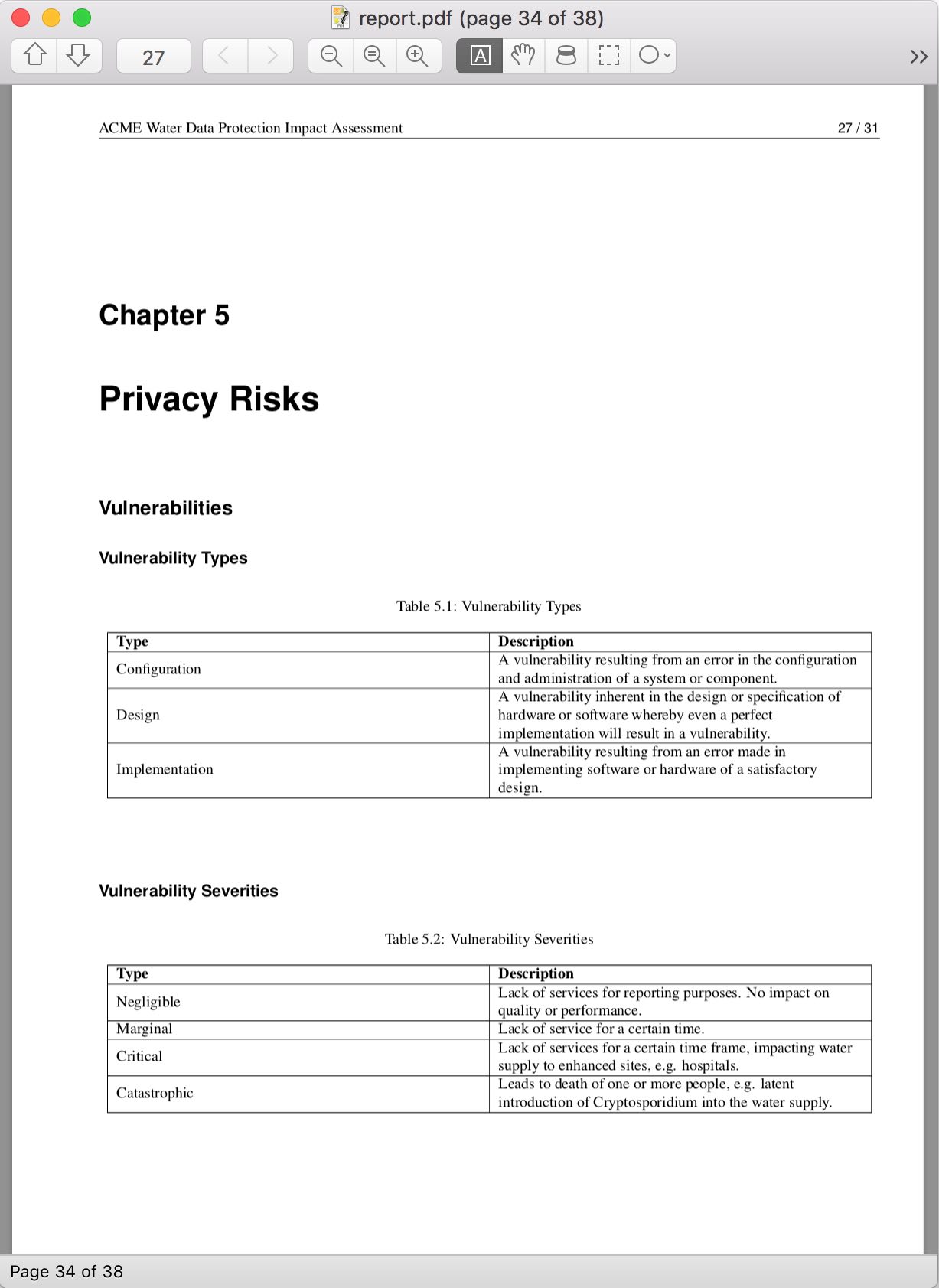
From assets to countermeasures, factoids to personas, and requirements to architectural components, enter or import a wide range of security, usability, and requirements data to find new insights ranging from interconnections between requirements and risks, to the justification behind persona characteristics.